HIPAA Compliance: A Common Sense Approach
 by Donna Vanderpool, MBA, JD
by Donna Vanderpool, MBA, JD
Ms. Vanderpool is Vice President, Risk Management at PRMS, Inc. in Arlington, Virginia.
Funding: No funding was provided for this article.
Disclosures: The authors reports no conflicts of interest relevant to the content of this article.
Reprinted with permission from Innov Clin Neurosci. 2019;16(1–2):38–41. © Copyright Matrix Medical Communications, 2019.
Answers in this column are provided by PRMS, Inc. (www.prms.com), a manager of medical professional liability insurance programs with services that include risk management consultation, education and onsite risk management audits, and other resources to healthcare providers to help improve patient outcomes and reduce professional liability risk. The answers published in this column represent those of only one risk management consulting company. Other risk management consulting companies or insurance carriers may provide different advice, and readers should take this into consideration. The information in this column does not constitute legal advice. For legal advice, contact your personal attorney. Note: The information and recommendations in this article are applicable to physicians and other healthcare professionals so “clinician” is used to indicate all treatment team members.
Question
I hear about breaches of medical privacy and Health Insurance Portability and Accountability Act of 1996 (HIPAA) fines nearly every day. These breaches typically involve large organizations, presumably with large information technology (IT) staffs. I have a small private practice with limited support staff and no in-house IT support. I take my professional obligation to protect patient confidentiality very seriously, but I often wonder how I can be expected to be held to the same standard as large organizations with all of their resources.
Answer
You bring up a valid point. Here are a few initial things keep in mind:
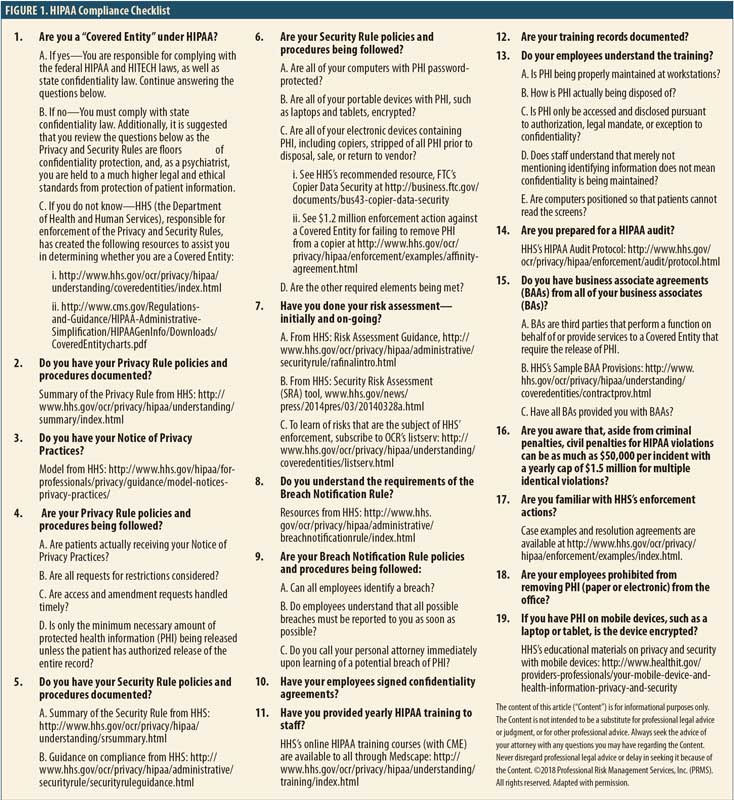
Are you even covered by HIPAA? Coverage under HIPAA basically is triggered by specific transactions with health plans done electronically. Only “covered entities” are required to comply with HIPAA and thus are subject to the government’s enforcement of HIPAA. See Figure 1 for more information on HIPAA’s applicability. However, even the entities that are not covered can have liability exposure for breach of confidentiality under the criminal provisions of HIPAA as well as under state law.
The Security Rule is scalable. The United States Department of Health and Human Services (HHS), responsible for HIPAA enforcement through its Office for Civil Rights (OCR), has stated that the Security Rule, covering electronic Protected Health Information (ePHI), is scalable. (Note that the Privacy Rules cover all Protected Health Information [PHI] verbal, paper, or electronic.) What the government might expect a large hospital system to do could differ from what a small practice might be expected to do. HHS has stated that “…the Security Rule is designed to be flexible and scalable so a covered entity can implement policies, procedures, and technologies that are appropriate for the entity’s particular size, organizational structure, and risk to consumers’ ePHI.”1
No amount of IT resources can prevent breaches involving blatant violations of patient confidentiality. Examples of recent HIPAA enforcement actions include:
Allowing the filming of television shows in hospitals without patient authorization. In 2016, a New York hospital entered a settlement agreement2 with OCR for $2.2 million for allowing ABC to film a television series “NY Med” in the hospital’s emergency department without authorization of the patients involved in the filming. The hospital was also sued by a patient’s family member who was horrified to see the death of their loved one on the show. Remarkably, two years later, three Boston hospitals entered a separate resolution agreement3 with OCR for $999,000. These hospitals also violated HIPAA by allowing television film crews on premises to film another ABC series “Boston Med” without patient authorization.
Allowing pharmaceutical sales representatives access to patient charts. A physician was arrested for, among other things, allowing drug representatives access to patient charts and lying to federal investigators. The physician was convicted4 of one count of violating HIPAA and one count of obstructing an investigation.
Releasing patient information to a reporter without authorization. A physician’s patient had contacted a local television station to discuss a dispute with the physician. The reporter then contacted the physician for comment. The privacy officer of the physician’s practice instructed the physician to either not respond or respond with “no comment.” Instead, the physician spoke with the reporter and impermissibly disclosed the patient’s PHI. After OCR investigated and found that the practice failed to take any disciplinary action against the physician, the practice settled with OCR for $125,000.5
Failing to terminate an ex-employee’s access to PHI. A hospital failed to terminate remote access to the web-based scheduling calendar that contained ePHI. OCR’s investigation found that the ex-employee had accessed PHI of 557 patients. The investigation also found that there was no business associate agreement between the hospital and the web-based calendar vendor, as required by HIPAA. The hospital paid over $111,000 as part of its resolution agreement with OCR.6
Sending human immunodeficiency virus (HIV) information to a patient’s employer without patient authorization. A patient who had received HIV treatment from a facility submitted an authorization form from his office fax, directing records to be mailed to his home address or his personal P.O. box. Instead of doing as authorized, the facility staff faxed the complete medical record to the patient’s employer. The patient complained to OCR. OCR investigated and found that the same facility was responsible for a different patient’s medical record being impermissibly disclosed months prior but had failed to address the vulnerabilities to prevent further breaches. The facility paid $387,000 to settle the case with OCR7 and was sued by the patient, who alleged negligence and negligent infliction of distress under state law.
Criminals are very interested in getting PHI. Reports of using malware to hold a provider’s ePHI for ransom are frequent. For more information in ransomware, see the HHS “Fact Sheet: Ransomware and HIPAA.”8 While there are many ways for criminals to access systems with ePHI, one way at which they are particularly proficient is phishing, or the fraudulent practice of sending emails purporting to be from a reputable company to obtain personal information. Anthem, a large insurance company, paid OCR $16 million in a record HIPAA settlement9 following the largest United States health data breach in history. PHI of close to 79 million individuals, including names and social security numbers, was stolen by cyber attackers. The criminals infiltrated their system through spear phishing emails; at least one employee responded to a malicious email and opened the door to further attacks. In addition to impermissible disclosure of ePHI, OCR found other violations, including a failure to conduct an enterprise-wide risk analysis. OCR has developed specific guidance on phishing attacks10 and on cyber security,11 including advice for small healthcare providers.
Five Key Actions to Stay HIPAA Compliant
Perform the HIPAA-required risk analysis and review and update periodically. In one case, the network of medical providers paid $3.5 million to OCR in settlement12 after reporting five breaches to OCR. Upon investigation, OCR found a failure to conduct an accurate and thorough risk analysis of potential risks and vulnerabilities to the confidentiality, integrity, and availability of all of its ePHI. (For resources, see the HIPAA Checklist.)
Train all employees on HIPAA’s requirements, your policies and procedures, and the potential for harmful phishing emails. Document the initial and annual training, and consider having employees sign confidentiality agreements.
Ensure you have business associate agreements (BAAs) from all of your business associates (BAs). HHS describes a BA as “a person or entity other than a member of the workforce of a covered entity who performs functions or activities on behalf of, or provides certain services to, a covered entity that involve access by the business associate to, protected health information.”13 Examples include, but are not limited to, answering services, billing services, and transcription services. Covered entities are required to enter into agreements (BAAs) with BAs to ensure that the BA will appropriately safeguard PHI. One physician group had to pay $500,000 to settle an OCR investigation,14 that found the group failed to have a BAA with the group’s billing service.
Protect all PHI, including special protections for ePHI. OCR expects all portable devices with ePHI, such as cell phones and laptops, to be appropriately encrypted. OCR investigated a Texas health system following three data breach reports involving the theft of an unencrypted laptop from an employee’s home and the loss of two universal serial bus (USB) drives containing the unencrypted ePHI of more than 33,500 individuals. The covered entity was ordered to pay $4.3 million in penalties.15 Other actions that protect ePHI include backing up ePHI appropriately and ensuring firewalls anti-virus protections are up to date.
If you think there has been a breach of confidentiality, contact your risk manager or medical malpractice insurance policy. Your insurance policy may include coverage related to HIPAA and other confidentiality violations.
References
- U.S. Department of Health & Human Services site. Summary of the HIPAA Security Rule https://www.hhs.gov/hipaa/for-professionals/security/laws-regulations/index.html. Accessed 6 September 2019.
- U.S. Department of Health & Human Services site. Unauthorized Filming for “NY Med” Results in $2.2 Million Settlement with New York Presbyterian Hospital. https://www.hhs.gov/hipaa/for-professionals/compliance-enforcement/agreements/new-york-presbyterian-hospital/index.html. Accessed 6 September 2019.
- U.S. Department of Health & Human Services site. Unauthorized Disclosure of Patients’ Protected Health Information During ABC Television Filming Results in Multiple HIPAA Settlements Totaling $999,000. https://www.hhs.gov/about/news/2018/09/20/unauthorized-disclosure-patients-protected-health-information-during-abc-filming.html. Accessed 6 September 2019.
- United States Department of Justice. Springfield Doctor Convicted by Jury of Illegally Sharing Patient Medical Files. https://www.justice.gov/usao-ma/pr/springfield-doctor-convicted-jury-illegally-sharing-patient-medical-files. Accessed 6 September 2019.
- U.S. Department of Health & Human Services site. Allergy practice pays $125,000 to settle doctor’s disclosure of patient information to a reporter. https://bit.ly/2Gr83Tr. Accessed 6 September 2019.
- U.S. Department of Health & Human Services site. Colorado hospital failed to terminate former employee’s access to electronic protected health information. https://bit.ly/2HUMzR2. Accessed 6 September 2019.
- U.S. Department of Health & Human Services site. Careless handling of HIV information jeopardizes patient’s privacy, costs entity $387k. https://www.hhs.gov/about/news/2017/05/23/careless-handling-hiv-information-costs-entity.html. Accessed 6 September 2019.
- U.S. Department of Health & Human Services. FACT SHEET: Ransomware and HIPAA. https://www.hhs.gov/sites/default/files/RansomwareFactSheet.pdf. Accessed 6 September 2019.
- U.S. Department of Health & Human Services site. Anthem Pays OCR $16 Million in Record HIPAA Settlement Following Largest U.S. Health Data Breach in History. https://www.hhs.gov/about/news/2018/10/15/anthem-pays-ocr-16-million-record-hipaa-settlement-following-largest-health-data-breach-history.html. Accessed 6 September 2019.
- U.S. Department of Health & Human Services. Phishing. https://www.hhs.gov/sites/default/files/cybersecurity-newsletter-february-2018.pdf. Accessed 6 September 2019.
- U.S. Department of Health & Human Services site. Health Industry Cybersecurity Practices: Managing Threats and Protecting Patients. https://www.phe.gov/Preparedness/planning/405d/Pages/hic-practices.aspx. Accessed 6 September 2019.
- U.S. Department of Health & Human Services site. Five breaches add up to millions in settlement costs for entity that failed to heed HIPAA’s risk analysis and risk management rules https://www.hhs.gov/about/news/2018/02/01/five-breaches-add-millions-settlement-costs-entity-failed-heed-hipaa-s-risk-analysis-and-risk.html. Accessed 6 September 2019.
- U.S. Department of Health & Human Services site. Business Associate Contracts. Sample business associate agreement provisions https://www.hhs.gov/hipaa/for-professionals/covered-entities/sample-business-associate-agreement-provisions/index.html. Accessed 6 September 2019.
- U.S. Department of Health & Human Services site. Florida contractor physicians’ group shares protected health information with unknown vendor without a business associate agreement. https://bit.ly/2HUNj8M. Accessed 6 February 2019.
- U.S. Department of Health & Human Services site. Judge rules in favor of OCR and requires a Texas cancer center to pay $4.3 million in penalties for HIPAA violations. https://bit.ly/2DXc9kI. Accessed 6 February 2019.
Category: Past Articles, Risk Management